
How Do You Pronounce Ledger? Pro…
How Do You Pronounce Ledger? Pronunciation Guide: practical reference notes for this topic (scope-specific to id=132001).How Do You Pronounce Ledger? Pronunciat…
Foundational knowledge about Ledger hardware wallets, offline signing, and the role of Ledger Wallet(原 Ledger Live).

How Do You Pronounce Ledger? Pronunciation Guide: practical reference notes for this topic (scope-specific to id=132001).How Do You Pronounce Ledger? Pronunciat…

Hardware Wallet vs Software Wallet|Storage Location, Confirmation, and Use Boundaries: practical reference notes for this topic (scope-specific to id=103103).T…

How Do You Say "Ledger Flex"?: practical reference notes for this topic (scope-specific to id=199023).How Do You Say "Ledger Flex"? explains the service scope, …
How to Say Ledger Flex | Model Name, Writing Form, and Comparison Context: practical reference notes for this topic (scope-specific to id=200982).Ledger Flex sh…

Ledger Sound and Chinese Approximation | From ledge to the Brand Name: practical reference notes for this topic (scope-specific to id=200981).Ledger can be expl…

Ledger IPA and a Simple Phonetic Approximation: practical reference notes for this topic (scope-specific to id=199016).Ledger IPA and a Simple Phonetic Approxim…
An Easy Way to Explain "Ledger" Pronunciation to Non-Native Speakers: practical reference notes for this topic (scope-specific to id=199026).An Easy Way to Expl…

Explaining Ledger Pronunciation to Chinese Speakers | Short Phrases and Use Cases: practical reference notes for this topic (scope-specific to id=200980).When e…

Ledger Pronunciation Guide | Sound, Stress, and Common Mix-ups: practical reference notes for this topic (scope-specific to id=200979).Ledger is commonly pronou…

Ledger Pronunciation Guide — IPA and Common Mispronunciations: practical reference notes for this topic (scope-specific to id=199013).Ledger Pronunciation Guid…

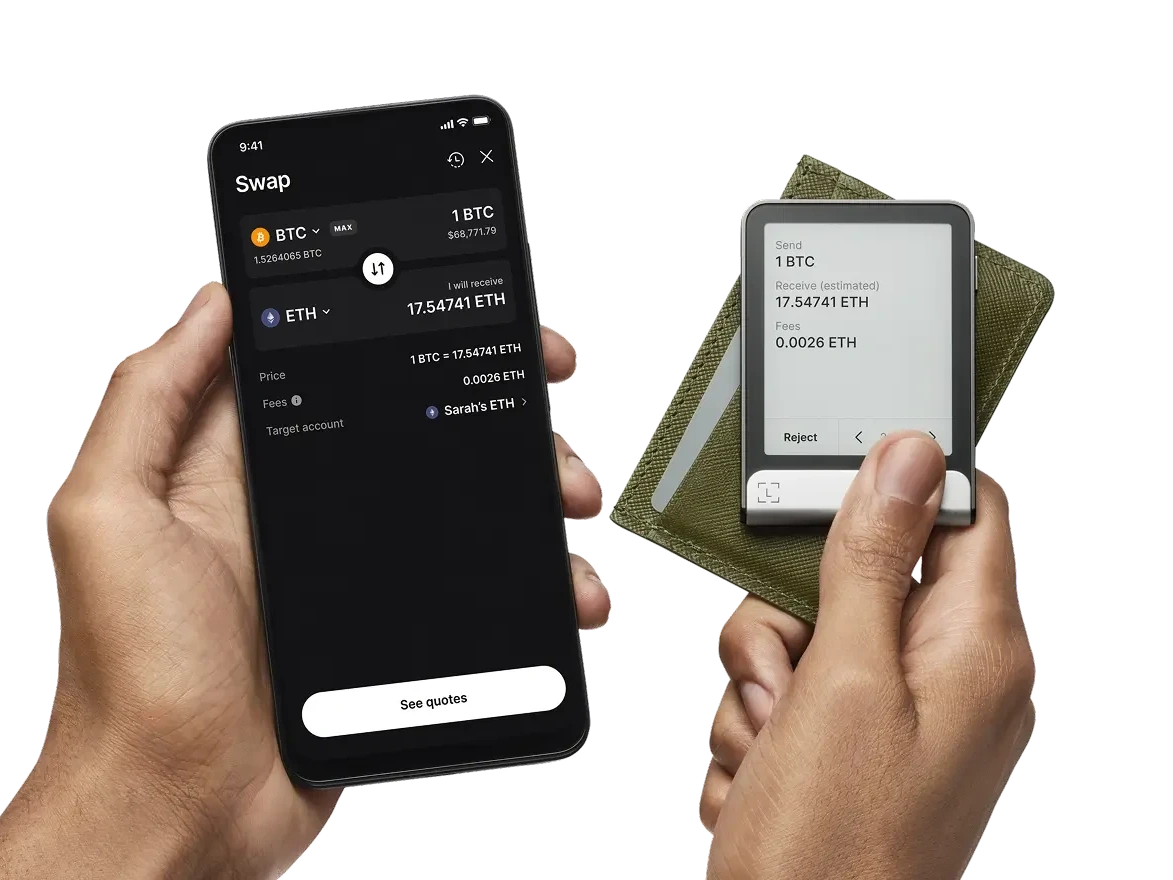
What a Ledger Hardware Wallet Is | Device, App, and Recovery Phrase Roles: practical reference notes for this topic (scope-specific to id=200978).A Ledger hardw…

Ledger 's Secure Element — How It Protects Your Assets: practical reference notes for this topic (scope-specific to id=131003).Ledger 's Secure Element — How …

Open WeChat and scan, or long-press to save the QR code